Cross-device identity has become an essential foundation for ad and marketing targeting.

From a Tapad video
Imagine you characterized the buying habits of customers by the cars they took to your physical store.
One person took a Ford pickup truck to buy a tuxedo, and, the next day, that same person took the family’s other car — a Volvo — to buy comic books and beer.
A similarly one-dimensional view of a customer’s interests takes place if you only look at behavior through one specific computer, smartphone or tablet. Increasingly, one can include in that mix such additions as a connected TV or a smart car.
My normal behavior, for instance, is to conduct almost all of my online shopping on a computer, with its larger screen. But I commonly use my smartphone to check particulars about movies or restaurants, since those decisions are often made when I’m out and about. And, if we could easily order our favorite Chinese delivery through our connected TV, I’m sure we would.
That’s why cross-device identity matching — resulting in a Device Graph — is the foundation underlying modern user profiling for digital marketing. A marketer can’t get a full picture of a customer or a would-be customer unless they know the activities on all the devices used by that person.
Two companies that specialize in Device Graphs are Drawbridge and Tapad. Others, like retargeter Criteo, develop extensive Device Graphs as necessary tools. And major marketing clouds like Oracle, Adobe and Salesforce develop their own or partner with vendors to make Device Graphs essentially part of their platforms.
Drawbridge Senior Marketing Manager Mike Murphy told me that all Device Graphs are built with the “same basic idea, but [each vendor’s] formula differs in how much weight is given” to specific attributes.
There are two main kinds of techniques — deterministic and probabilistic — and many Device Graphs utilize both to some degree.
Deterministic, probabilistic
Deterministic techniques are considered a gold standard, since they can be expected to definitively show which user is attached to which device. That is generally accomplished through a logon.
If you regularly enter your username and password into a site from your smartphone, for instance, that brand knows this user profile — meaning, this user — is associated with this device. (Allowances are made for occasional entries of that logon from other devices, which might be a computer at work.)
Probabilistic techniques combine data points to make reasonable assumptions about device ownership.
Murphy noted that common probabilistic data points include the times of day when the devices are used, their physical locations at night as indicated by IP addresses, WiFi or 3G/4G characteristics, regular browser characteristics for web surfing, browsing patterns and other attributes.
He noted that Drawbridge can identify device use down to individuals, even if the devices sometimes share the same household. The smartphones and laptops of two college-aged siblings, for instance, might share the same physical location at night in the summer but depart for separate college towns during the school year.
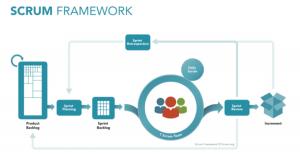
Here Tapad depicts the Device Graph process, largely portrayed through probabilistic technique, although Tapad uses both:
Device Graphs often employ a combination of deterministic and probabilistic methods. For instance, a user’s collection of devices might be determined with a high degree of accuracy if only one of them was used to logon to a participating brand’s site.
That one device — such as a smartphone — becomes the definitive association, and others — say, a laptop and a tablet — are found to reside at night in the same location as the phone, and they visit the same sites daily. These and other signals lead the Graph-maker to determine they all belong to the same user, even though there has been only one device logon.
Other data layers
While deterministic-based associations with devices approach 100 percent accuracy, probabilistic ones can also have very high accuracy rates. Vendors commonly claim probabilistic rates north of 80 to 90 percent.
Once a user’s constellation of devices is known, marketers can then authoritatively connect that user to other data layers in order to widen that user’s profile.
A physical loyalty card at Target, for instance, might be connected via an email address to at least one device, which can then be connected to that user’s other devices. Persistent identifiers like email addresses are often used to connect Device Graphs to other layers, but other coincident data points might be used as well.
Email addresses are usually hashed into coded labels. If the same hash table is used, the same email address will generate the same hashed code even if it comes from different devices or other sources, so they can be matched anonymously.
And Device Graphs help make sense of the dark arts of attribution. If your smartphone is used when you purchase sneakers on sale at a shoe store, for instance, ads for that sale delivered to your associated laptop can be given at least some credit for driving the sale.
Retargeter Criteo considers Device Graphs to be such an essential tool to its business that it has built what SVP of Product Management Patrick Wyatt told me is the largest “global scale mapping of email addresses to cookies,” except for the giants, Facebook and Google.
‘Just another device’
By defining the devices you own into one group, Criteo can then link them via a shared email address to a profile in a client company’s customer relationship management (CRM) system, thus revealing that these devices are owned by this customer or would-be customer of the brand.
Both Criteo’s Wyatt and Drawbridge’s Murphy envision that Device Graphs will continue with the deterministic/probabilistic model for the indefinite future.
One possible exception to this, of course, would be if biometric identification became the norm for using your device and perhaps for logging into sites or apps. In which case, hashed biometrics could deterministically identify every device you own.
But, notwithstanding that possible future, Wyatt thinks the biggest evolution of Device Graphs will be how they are used to connect with other kinds of data layers, especially new kinds of offline activity.
There are countless offline activities which are still unconnected to your device constellation, but, as the Internet of Things continues its growth, their linkage could be just a matter of time.
As Wyatt told me, citing an observation by a colleague at Criteo: “Offline is just another device.”’
Marketing Land – Internet Marketing News, Strategies & Tips
(48)