Managing the personal use of the internet by employees is a considerable challenge. Should employees be allowed to use business internet for personal reasons? How much personal use is too much? How can you offer personal use of the internet as a workplace perk without negatively affecting productivity and security?
In this article I will cover common concerns related to personal use in the workplace, overview the benefits of allowing personal use, and provide tips for addressing personal use in your workplace computer use policy.
Table of Contents
- Should You Let Employees Use the Internet for Personal Tasks?
- The Risks of Allowing Personal Internet Use in the Workplace
- Why Let Employees Use Company Devices for Personal Use?
- Best Practices for Managing Personal Use of the Internet at Work
- What’s Next?
Should You Let Employees Use the Internet for Personal Tasks?

Deciding whether or not to allow your employees to use the internet for personal tasks is not as clear-cut as it may seem. There are a number of privacy and security concerns associated with personal internet usage.
For example, personal email accounts are more vulnerable than those protected by corporate email gateways. Employees that are being monitored on corporate systems may have sensitive information captured by the employee internet management software.
On the other hand, zero-tolerance policies for personal web browsing are likely to frustrate employees and negatively impact morale. When developing your computer use policy you must consider how you will balance network security, productivity, and employee satisfaction.
The Risks of Allowing Personal Internet Use in the Workplace
Lost Productivity From Excessive Cyberloafing

For most workplaces a little bit of web surfing between tasks is no issue. That said, without a formal structure some employees can abuse this privilege.
But how much is too much?
According to a publication from Brent Coker of the University of Melbourne so-called “cyberloafing” can have a positive impact on employee productivity; so long as non-work internet browsing does not consume more than 12% of an employee’s work time.
“Short and unobtrusive breaks, such as a quick surf of the Internet, enables the mind to rest itself, leading to a higher total net concentration for a days’ work, and as a result, increased productivity.”
Brent Coker, lecturer of Marketing, University of Melbourne
If excessive web browsing (“cyberloafing”) is affecting productivity that doesn’t necessarily mean that employees should be forbidden to use the internet for personal use altogether.
Computer use policies that are too restrictive will just annoy employees and tempt them to spend more time trying to hide their web browsing than they would actually spend browsing. The key here is to set clear expectations, define how productivity will be measured, and foster an environment that emphasizes employee autonomy.
I will touch on the best practices for balancing productivity and cyberloafing later in this article.
What is cyberloafing?
Cyberloafing—also known as cyberslacking— describes when an employee surfs the web for reasons that are not related to their job. This includes using workplace internet for personal use, playing computer games, and browsing social networking sites.
Why do employees cyberloaf in the workplace?
- 34% of employees say they are not challenged enough
- 34% say they work long hours
- 32% say there are no incentives to work harder
- 30% are unsatisfied with their employment
- 23% say they’re bored at work
- 18% say it’s due to low wages
– Salary.com: Wasting Time at Work Survey 2013
Network Performance Issues From Bandwidth Hogs

Your business needs a reliable and smooth internet connection to thrive. If employee web surfing is congesting your network you will need to address their use of bandwidth hogs accordingly.
Common bandwidth hogs include:
- Movie streaming sites like Netflix, Prime Video, and Disney+
- Video sharing sites like YouTube, Vimeo, and Dailymotion
- Live streaming sites like Twitch, Facebook Gaming, and YouTube Gaming
It’s important to note that not all high-bandwidth websites are exclusively used for personal or unproductive reasons. An employee could have a legitimate business reason for browsing YouTube at work such as watching video tutorials or listening to music, TED Talks, and other valuable content.
That said, your network needs to remain fully operational so that it can be used for its intended purpose. You need to find that balance between allowing personal use of the internet without affecting overall productivity and network efficiency.
Depending on the needs and capabilities of your network this could be as simple as requiring that high bandwidth websites such as YouTube are used exclusively for business purposes.
If your employees have designated break periods your computer use policy could allow for some degree of personal use so long as it’s not negatively affecting the productivity of their coworkers.
For employees that need music to focus they can be provided with alternatives such as low-bandwidth music streaming services or being permitted to use their personal cell phones to listen to music.
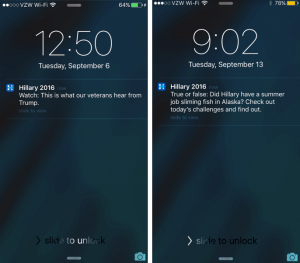
Cybersecurity Risks From Personal Internet Use
Source: Spiceworks
Providing employees with unrestricted internet access is a cybersecurity nightmare. The internet is rife with security threats like phishing emails, malware, and threat actors that would love nothing more than to compromise your organization’s network.
Security risks of employee web browsing:
- Data theft: A disgruntled (or negligent) employee could easily log in to a personal cloud storage site and transmit sensitive data to an external server.
- Malware: Employees that browse the internet unimpeded are more likely to run into high-risk sites and download potentially compromised files.
While there is certainly no shortage of danger when networks are used exclusively for business purposes, personal web browsing is naturally higher risk. This is particularly true if employees are using their personal email accounts at work as these accounts are unlikely to be as secure as ones that are managed by the company.
Social media websites also pose a significant risk; as seen in the above graph from Spiceworks they were responsible for 11% of security incidents.
Why social media is particularly dangerous
- Malware is spread on social media through links, often with catchy headlines
- Social media sites are another avenue for phishing and social engineering attacks
- Many social networking sites let users upload and share content, increasing the risks of accidental or malicious data leakage.
The types of websites an employee would visit for work purposes are likely to be pre-vetted and reasonably secure, whereas unfamiliar sites could pose a security risk. Depending on the level of personal use permitted there is also the risk of employees downloading risky software onto company computers.
Legal Liability For Piracy And Other Illegal Activity

As an employer you are responsible for ensuring that your employees use company-provided resources appropriately.
If your employees use the internet for illicit purposes such as piracy, data theft, harassment, hacking, and related activities there is a significant risk that your company will be held liable for any associated damages.
Blurring the lines between personal and professional may cause some employees to engage in unsavory behaviors that contribute to a hostile work environment. When allowing employees to use workplace equipment for personal reasons it’s critical that professional expectations are maintained.
Depending on the workplace privacy and employee monitoring laws of your jurisdiction allowing personal use can also be a liability issue as sensitive personal information could be captured by your company’s workplace surveillance software.
Which leads us to…
Potential Impacts on Employee Privacy

Employee monitoring software does not make any distinction between personal and business use. When monitoring employees in the workplace it is critical that they understand exactly what is being monitored, how their data is being used, and who will have access to it.
On a surface level, the majority of employees are likely to understand that their employer can see anything they do on corporate systems. That said, ambiguity over how much is being monitored could lead to employee privacy concerns.
What is being monitored, exactly?
- Standard internet usage activity such as bandwidth usage and URLs visited, or;
- Invasively intimate details such as individual keystrokes and private conversations?
Full transparency of employee monitoring ensures that employees that use workplace equipment for personal reasons are making an informed decision. Depending on the laws of your jurisdiction you may even need to adjust what is being monitored to reduce impacts on employee privacy.
Why Let Employees Use Company Devices for Personal Use?
With all of the risks of letting employees use company devices for personal use you may be tempted to forbid the practice altogether. After all, why would you let employees use company devices for personal use if it’s going to require so much forethought?
In this section I’d like to discuss why allowing personal use of company devices can be a good thing for your organization. After that I’ll provide you with some best practices so you can balance the risks vs rewards of personal use.
It’s Good for Employee Morale
Source: Spiceworks user ICH
When developing your computer use policy you must consider how you will balance network security, productivity, and employee satisfaction.
Computer use policies that are too restrictive are frustrating for employees. As individuals employees want to feel that they are trusted to manage their own productivity. Allowing for a reasonable amount of personal use provides employees with the autonomy to self-manage.
Besides, employees spend a significant portion of their lives at work. Allowing for some flexibility helps employees maintain a suitable work/life balance and increases overall workplace satisfaction.
It’s a Great Job Perk

While high-speed internet is becoming increasingly more available and affordable, there are still those that do not have reliable internet access at home.
Internet infrastructure for rural communities is underdeveloped on a global scale. According to the report Measuring digital development: Facts and figures 2020 from the International Telecommunication Union, global home internet access is nearly twice as high in urban areas as it is in rural areas: 72% of urban households have access to the internet, yet this is true for only 37% of rural households worldwide.
For some employees having reliable internet access at work provides them with opportunities that they would not otherwise have. Employers with flexible computer use policies are highly desirable for these candidates.
Aside from that, employees that frequently travel for work are going to have plenty of off-hours time that they need to fill up. Carrying around two laptops is certainly a hassle; in these sort of situations the employee may even expect that they can use their work devices to keep entertained in their downtime.
They’re Going to Do it Anyway

Even if personal internet use is not permitted in your computer use policy, there’s a strong chance that employees are going to do it anyway.
Consider this…
- 97% of male survey participants and 85% of female participants in a survey from Singapore Management University believed that cyberloafing in the workplace was acceptable.
- 64% of employees in a Salary.com survey admitted to visiting non-work related websites every day while at work.
- 71% of employees in the Salary.com survey believe that short breaks throughout the day are beneficial for their productivity.
Worse yet, overly restrictive policies can actually be a security risk. If too many of the websites that your employees want to visit are being explicitly blocked they are more likely to seek out ways to bypass your web filter. This opens your network to high-risk websites, phishing emails, and other web security risks.
While there certainly needs to be clear guidelines, banning personal internet use altogether might not be the best solution. Alternatives such as limiting personal use to break times, defining what types of personal use are allowed, and setting clear productivity expectations may be better suited.
Best Practices for Managing Personal Use of the Internet at Work
Create a Computer Use Policy
A computer use policy is a must-have for any organization that provides their employees with access to computers. Companies that have rules regarding their employee’s personal use of the internet will use a computer use policy to communicate their expectation.
A computer use policy is used to:
- Outline security standards and best practices such as password management practices, lockout policies, and web browsing expectations.
- Set a precedent for corrective actions the company will take when employees use workplace technology inappropriately.
- Disclose the employer’s intent to monitor employee computer activity such as internet and application usage, emails, and data handling.
How to Write the Perfect Internet Use Policy
- Avoid being too detailed
Outline the most common misuses you are guarding against such as illegal activity, workplace harassment, and other related actions that would be harmful to your business. You don’t want to be too broad though. A vague phrase like “Inappropriate use is prohibited” isn’t going to cut it – be sure to provide enough detail to limit ambiguity without going overboard. - Use strong, active words
When outlining explicit employee expectations in your policy you must use strong words such as must rather than should. This makes it clear that what is being asked of them is a rule rather than a general guideline. - Test your employee’s knowledge
After your employees read the policy you should ask them pointed questions to ensure they have truly read and understood the policy rather than simply signing it blindly. - Keep the policy in an accessible location
After they’ve read and signed the policy, show your employees where they can go if they need to access it again. Keep copies of the policy in a convenient location such as the company intranet and the employee handbook. After all, the intent of the policy is to communicate expectations; it’s not simply a piece of paper that’s intended to be buried in a file somewhere out of reach. - Use text formatting and organization to your advantage.
Break large blocks of text into smaller sections, use headers to separate key sections, and use typefaces that are easy to read. Making the policy skimmable will help greatly when employees need to refer back to it to remind themselves of specific stipulations.
What Employees Should NOT Do on Work Computers
Even when personal use of workplace equipment is allowed, there needs to be clear professional boundaries. Setting reasonable boundaries such as these in your workplace computer use policy will help to ensure that personal use doesn’t become a productivity, security, or liability concern.
1) Don’t Download Unauthorized Software

Allowing employees to download software onto their work computers is incredibly risky. There is no shortage of related risks such as software piracy, shadow IT usage, and added labour costs from IT departments needing to factor in unanticipated elements during troubleshooting.
Besides, employees should not be provided with administrative privileges on their computers in the first place. This provides far too many opportunities for employees to become an entryway for malicious cyberattacks that spread throughout the corporate network.
2) Don’t Save Personal Files to Work Devices

Employees that regularly use work computers for personal use are going to be tempted to save personal files to the hard drive.
If left unchecked this habit can lead to the loss of important personal documents, inflated storage use, and a greater potential for infected documents to find their way to company devices.
Employees that get a little too comfortable with saving personal documents on their work computers may also inadvertently store particularly private files that they’d rather not provide others with access to. If they are unexpectedly terminated and locked out from their machine before they can delete their data this could cause serious privacy concerns.
3) Don’t Save Personal Passwords on Company Devices

It’s critical that employees avoid saving their passwords to company devices. Depending on your network infrastructure allowing them to save their credentials could compromise the security of their accounts. Considering how online banking is a common use-case for computers it’s immediately clear that this is a serious personal security issue.
In addition to officially supported password managers, many modern web browsers include an integrated password manager. As a best practice companies should disable password caching on web browsers to avoid having login credentials available outside of an approved channel.
4) Don’t Connect Work Devices to Public WiFi Hotspots

According to the 2018 iPass Mobile Security Report, 81% of CIOs said their company had experienced a WiFi related security incident in the last year, with 62% of WiFi related security incidents occurring in cafés and coffee shops.
Insecure public WiFi hotspots are attractive to attackers as the volume of people connected to the network and the lack of encryption on some websites allows them to monitor the internet traffic of anyone connected to the network.
Attackers may also use a type of man in the middle (MitM) attack known as a “honeypot” to trick users into establishing a connection with their network device by masquerading as a legitimate WiFi hotspot.
In addition to this, the security of a legitimate public network is not guaranteed. These wireless access points are managed by a third party and they are often provided as a convenience to the public rather than for sensitive business purposes.
To mitigate the temptation to use these insecure WiFi hotspots, remote workers should have their own mobile router or high-speed mobile data plan. A mobile router transforms 4G or 5G wireless connections into a private WiFi signal, negating the need to use potentially unsecured WiFi networks.
What Is a Man in the Middle (MitM) Attack?
A man in the middle (MitM) attack is when a threat actor intercepts or alters communications between two parties. These types of attacks are typically used by threat actors to gain information during the early reconnaissance stages of a more advanced attack.
5) Don’t Do Anything You Wouldn’t Like Your Employer to See

Even if personal use is permitted on work devices employees must avoid saying or doing anything on a work-issued computer or account that they don’t want their employers to see.
Paying the odd bill from time to time or sending a brief personal message to a loved one may be fine, but it’s best to avoid doing anything unprofessional. Depending on what sort of computer activity is being monitored inappropriate internet behaviors on company property could become a liability issue.
Provide Employees With Cybersecurity Awareness Training

This particular tip is true regardless of whether or not employees will be using work issued devices for personal reasons. You simply cannot afford to skip out on cybersecurity training for any and all staff members that interact with technology in the workplace.
Threat actors routinely take advantage of human error and deception to compromise information systems and assets. Providing employees with security awareness training is incredibly valuable as it reduces the chance that employees will fall for phishing schemes and engage in high-risk behavior.
While the exact ROI of a cybersecurity awareness program is difficult to measure precisely, there’s zero doubt that it’s non-negotiable for any business that takes data security seriously. When it comes to permitting personal use ensuring that employees are equipped with the knowledge they need to browse safely is paramount.
Decide How Much Personal Use Should Be Allowed

It’s important that you are explicitly clear as to what sorts of personal activities will be permitted on company devices. The general concept of “personal use” can be used to describe casual web surfing just as much as it can describe running a side business using company assets.
Setting clear expectations in advance will help employees better understand what is expected of them. How specific or vague you make your computer use policy is up to you, but if you simply state that “excessive personal use” and “inappropriate browsing activity” are forbidden without any sort of guidelines there may be too much ambiguity.
That said, you will not necessarily need to explicitly detail every possible scenario. Just consider what types of activities you are guarding against and provide enough information to clearly communicate your expectations.
Decide where you’ll draw the line:
- Moonlighting: Are employees permitted to work on freelance projects using company devices? If so, who truly owns the copyrights to the work that is produced?
- Entertainment: Can employees stream movies, listen to music, and read for leisure on company equipment? If so, are there any restrictions such as only partaking after work hours?
- Social Media: Can employees use social media and other channels to communicate with family and friends? Is there a limit to how active they can be on social media during work hours?
- Errands: Is personal banking, online shopping, and other personal tasks permitted? Are there any privacy or security considerations that your employee should be aware of?
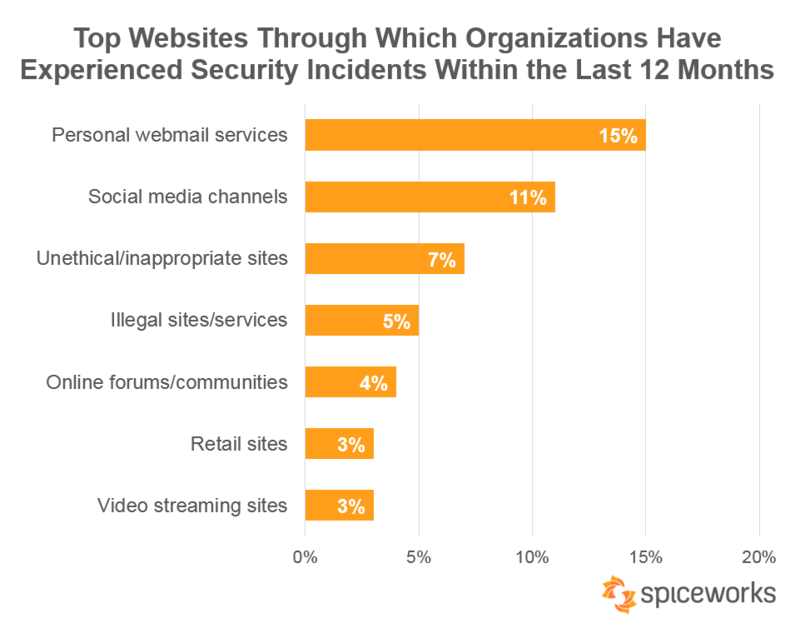
Should Companies Restrict Internet Access?
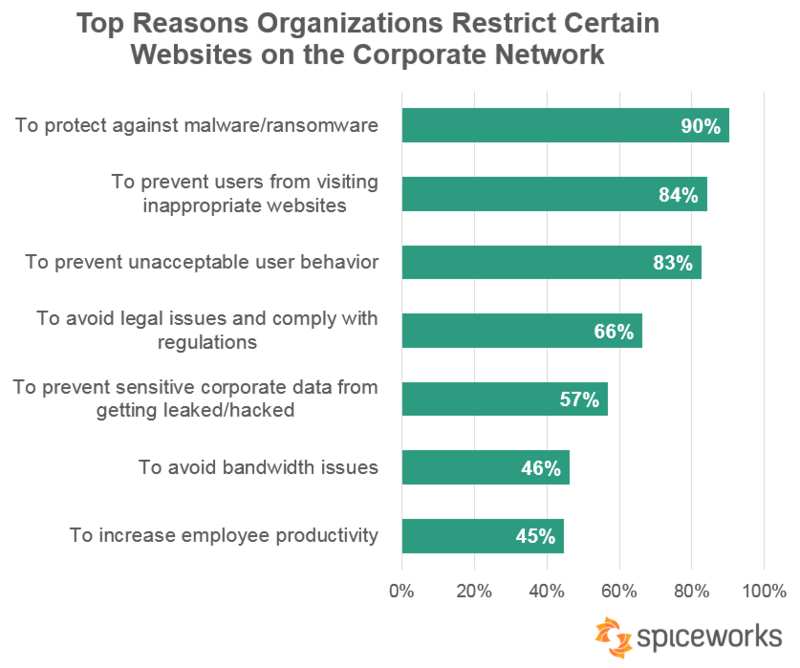
Source: Spiceworks
According to Spiceworks research, 89% of organizations block?or limit the use of one or more online service/site, such as social media, streaming services, or online shopping.
The top reasons for restricting employee internet access include protecting against malware (90%), preventing users from visiting inappropriate websites (84%), and to prevent unacceptable behavior (83%).
Interestingly, only 45% of respondents block websites to increase employee productivity. If you decide to block non-work websites for this reason you may want to consider scheduling more relaxed internet restrictions during employee break times.
When using web filtering for employee productivity it’s important to recognize that there needs to be a balance between security and productivity. Overzealous internet restriction policies may incentivize employees to seek ways of accessing blocked websites, negating the security benefits of a web filter.
Should Companies Monitor Employee Internet Usage?
“Employers that don’t monitor [their employees] will become fewer and fewer, not to nail employees, but because monitoring increasingly makes business sense.”
Manny Avramidis, president and CEO, the American Management Association
Monitoring employee computer activity is incredibly common. According to a Spiceworks survey of 550 IT pros a solid 91% of organizations monitor employees in some way.
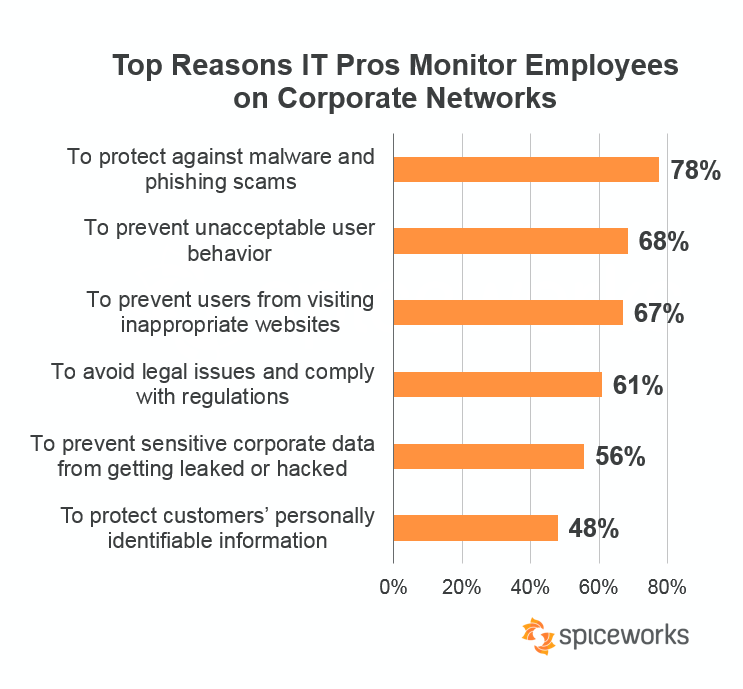
Source: Spiceworks
The survey data shows that the majority of IT departments monitor employee activity to protect companies from malware and phishing scams (78%), prevent unacceptable behavior (68%), stop users from visiting inappropriate websites (67%), and protect companies from legal issues (61%).
Internet monitoring software was found to be the most common method for monitoring employee activities, with 78% of organizations in another Spiceworks survey opting to use it.
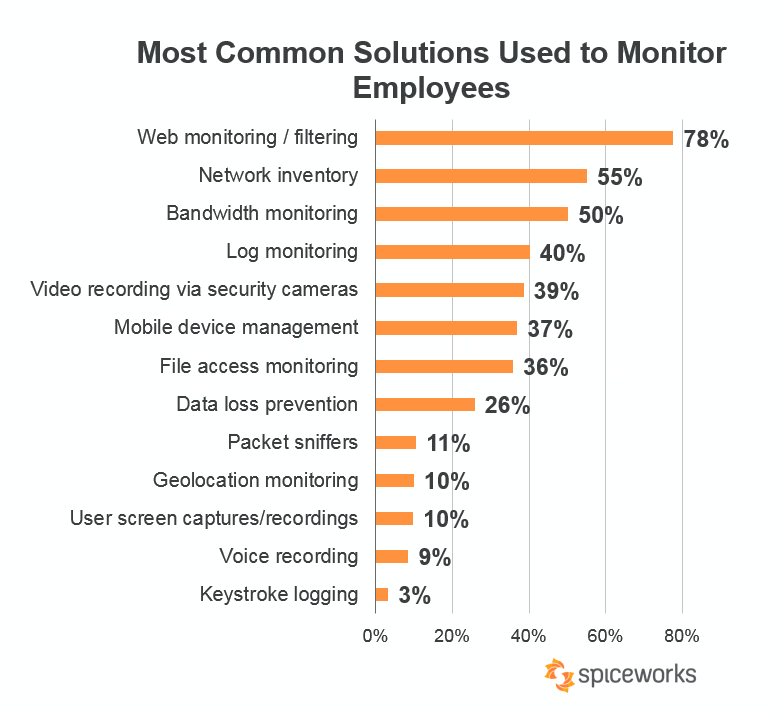
Source: Spiceworks
When using web monitoring software in the workplace it’s important to realize that there’s no way to reliably discern between personal and professional use of the internet. If your employees will be allowed to use company devices for personal use you will need to be well versed in the workplace privacy laws of your jurisdiction.
In some jurisdictions employees that use work devices for personal use may have legitimate protected privacy expectations. As a general best practice you must inform your employees that their computer activity will be monitored in advance so they can limit their personal use accordingly.
You can also configure your employee monitoring to only monitor employee computer activity during work hours. This allows employees the opportunity to freely browse during their breaks and other periods where personal use would be considered acceptable.
What’s Next?
Managing the personal use of the internet by employees is a considerable challenge. By following the best practices in this guide you will be able to create a computer use policy that balances your organizations legitimate productivity and security concerns with the desires of your employees.
If you would like a head start in creating your own computer use policy you can download our free internet use policy template and customize it to fit the needs of your business.
Business & Finance Articles on Business 2 Community
(115)